And Who is Afraid of Not Having One?
|
December 2013 |
[an error occurred while processing this directive] |
|
What is a
Security Fabric?
And Who is Afraid of Not Having One?
|
| Articles |
| Interviews |
| Releases |
| New Products |
| Reviews |
| [an error occurred while processing this directive] |
| Editorial |
| Events |
| Sponsors |
| Site Search |
| Newsletters |
| [an error occurred while processing this directive] |
| Archives |
| Past Issues |
| Home |
| Editors |
| eDucation |
| [an error occurred while processing this directive] |
| Training |
| Links |
| Software |
| Subscribe |
| [an error occurred while processing this directive] |
We’re exposed - and the voices pointing it out are getting loud. The editorials, product announcements and demo-project progress reports released this October and November about Industrial Control System cyber-security comprise a critical mass of attention, and hopefully, progress in covering our vulnerabilities.
Both the industrial automation and building automation industries are decades behind the times when it comes to security. Despite high-profile breaches, little progress has been evident. Among all the innovators represented in the Groom Energy chart of the Energy Smart Grid Vendor Landscape there are no cyber-security vendors or even a category. Is cyber-security such a mega-trend that it doesn't need mentioning? Can you bring it up when you ask why the market for these emerging, transformational technologies is stalled? Customers know their supervisory control and data acquisition (SCADA) systems and building automation systems (BAS) are easily penetrated by hackers and malware developers. In his November article in Chief Engineer, Brad Witter, EVP of Technology and Operations at Blue Pillar, cites brand-name analyst studies when he states "cyber-security threats piggyback upon retrofits." Newer energy management systems and building automation systems introduce more risk because they rely more heavily on Internet connectivity.
Stuxnet is the one case that has received national news coverage. But, there is underlying awareness that many more similar attacks have happened, with those in the know stifling attention in the interest of national security. The fact that digital chat on the topic is gaining volume bodes consensus, leadership and action on a more secure way forward.
The interview with Fred Gordy of Atlanta-based BAS integration firm McKenney’s in the CNBC news brief on ‘Hacking America’ was eye-popping. McKenney’s has been running a honeypot experiment to draw out would-be industrial control systems attackers. Gordy reports that in about six months there has been some 30,000 unauthorized attempts to breach the system, most originating in China, Russia, the Netherlands and Iran. This experiment is run with supervision from Cylance, a cybersecurity technology and services firm with close ties to the U.S. Department of Homeland Security’s Industrial Control System - Computer Emergency Readiness Team (ICS- CERT). Another BAS integration leader and independent software vendor, Lynxspring, in collaboration with remote software solution provider Netop, just introduced LYNX CyberPRO. This packaged software hardens the firewalls around building automation and energy management systems by removing exposed devices and ports from the public Internet, among other security management functions. Lynxspring spokesperson, Mark Petock, has relentlessly reminded his industry peers that "Gone are the days of security through obscurity."
Frost & Sullivan is among the analyst firms that have active ICS cyber security practices. According to Senior Analyst Karthik Sundaram in a 2012 article in Remote Magazine, “In order to effectively mitigate cyber-attacks, end-users need to adopt a comprehensive security framework that includes fundamental changes in policy formulation, establishment of an industrial cyber workforce, multi-level network protection and pro-active threat assessment.”
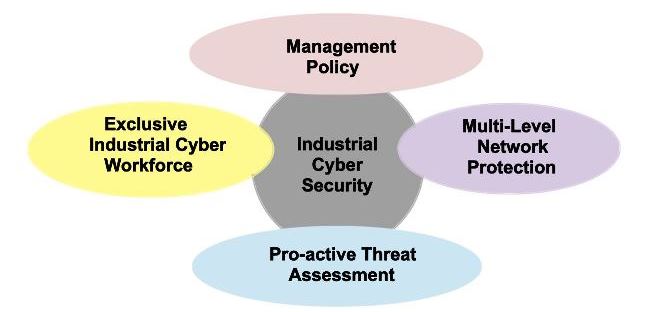
Diagram Credit: Frost & Sullivan, Europe
McKenney’s is already organized to deliver on the workforce and policy aspects of cybersecurity by offering training in best practices, security assessments and incident response. Other forward-thinking ICS integration firms will do the same for their customers, potentially addressing the three primarily 'human-factor' ICS cyber-security must-have's diagrammed above.
[an error occurred while processing this directive] Regarding the fourth 'machine-factor' issue — Multi-level Network Protection — the Security Fabric Alliance has an approach it demonstrated within the Smart Grid Catalyst project unveiled at the 2013 TM Forum Digital Disruption conference. This approach involves baking in embedded security (Intel McAfee-developed) as a block at the system-on-a-chip design phase of every connected intelligent device. Such hardware-level protections are then augmented by communications-layer security. A different approach toward the same goal was announced in November by Verizon Enterprise Solutions. Verizon’s Managed Certificate Services (MCS) platform is a pay-as-you-go cloud-based service to authenticate the identity of devices, such as smart meters, and to secure data transmissions when they attempt M2M communications over Verizon networks.
Both
approaches point to a future wherein SCADA and control systems
cannot talk to the power grid unless their identity and security status
is recognized and approved in the handshake. Likewise a controller
won't talk to a gateway or router until the same verification step
happens, and so on down to every microprocessor-equipped sensor device
in an HVAC or lighting network. Widespread adoption of such end-to-end
security fabric approaches will take whole-industry participation
and
the sponsorship of international governments, but such a level of
attention and engagement feels appropriate to the scope and nature of
the ICS cyber-security threat.
About the Author
Therese
Sullivan, Principal, www.buildingcontext.me
Engaged in brand building, social media community organizing and
content creation for some great minds in building energy efficiency.
Led the awareness campaign for the IDeAs Z-squared facility, an
Integral Group net zero energy commercial project - one of the first in
the nation.
[an error occurred while processing this directive]
[Click Banner To Learn More]
[Home Page] [The Automator] [About] [Subscribe ] [Contact Us]